
Comprehensive Approach to Printer Security
Supporting Zero Trust Security to Protect Printers and Data
Security for People Who Aren't Wired for Constant Data Protection, Part 2
Security for People Who Aren't Wired for Constant Data Protection, Part 2

Security for People Who Aren't Wired for Constant Data Protection, Part 1
Security is a top priority for us, and we know it is for your business, too. That’s why every Xerox® ConnectKey® Technology-enabled device is armed with our holistic four-point approach to security, ensuring comprehensive, all-encompassing protection for all system components and points of vulnerability.
Security Features
1. Prevent
A comprehensive set of capabilities prevents malicious attacks, proliferation of malware, and misuse of unauthorized access to the printer. Whether from transmitted data or directly at the MFP, all access points are protected through user authentication and access controls.
2. Detect
A comprehensive Firmware Verification test, either at start-up* or when activated by authorized users, provides alerts if any harmful changes to the printer have been detected. Trellix Whitelisting** technology constantly monitors for and automatically prevents any malicious malware from running. Integration with Cisco® Identity Services Engine (ISE) auto-detects Xerox® devices on the network and classifies them as printers for security policy implementation and compliance. By interacting with the market-leading Trellix DXL and Cisco® pxGrid platforms, Xerox multifunction printers (MFPs) employ an orchestrated response that neutralizes threats at their source the moment they occur.
*VersaLink devices **AltaLink, VersaLink 7100 Series, EC7800/8000 Series, and iSeries MFPs
3. Protect
Capabilities prevent intentional or unintentional transmission of critical data to unauthorized parties. Documents are not released until the right user is at the device and scanned information is protected from unauthorized users. Xerox also protects stored information, using the highest levels of encryption. Processed or stored data that is no longer required can be deleted using National Institute of Standards and Technology (NIST) and U.S. Department of Defense approved data clearing and sanitization algorithms.
4. External partnerships
ConnectKey Technology provides extra security standards through our partnerships with Trellix* and Cisco®. We measure our performance against international standards with certifications like Common Criteria and FIPS 140-2 to ensure our devices are trusted in even the most secure environments.
*AltaLink devices

Product and Data Security Solutions at Xerox
Security is critical to every business, and we take it seriously at Xerox.

Zero Trust Security for Printers
Cybercrime has reached unprecedented levels globally, and is expected to continue growing. Organizations need new strategies and best practices to defend against these threats.
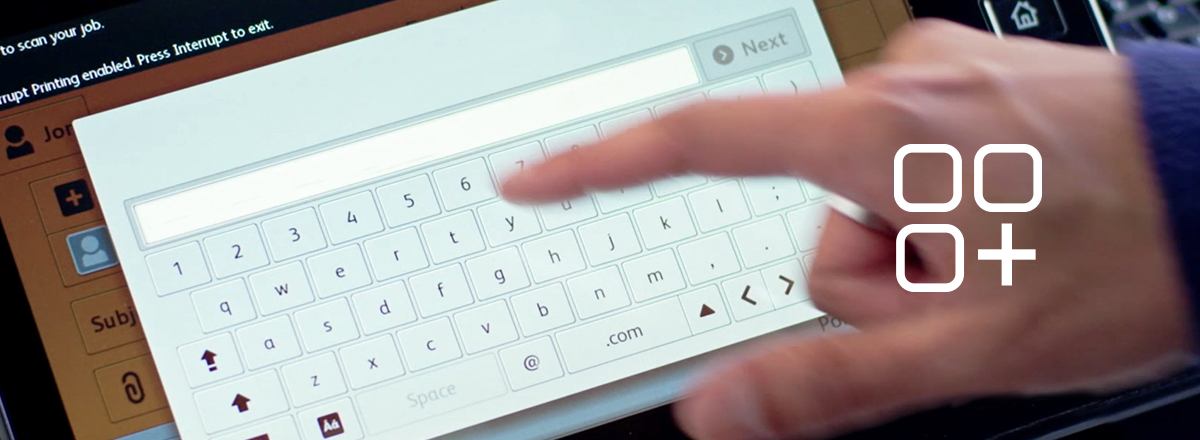
ConnectKey in Action

Print from the cloud
See how Robert downloads, scans, prints, shares, and translates docs from his mobile device to the MFP.
Use apps for tasks
See how a bank replaces time-intensive manual tasks with custom apps that speed processes.

Creating E-Documents
Read about how a hospital converts hard-copy records to digital and accesses them from the cloud.